In the aftermath of the 2001 terrorist attacks on the World Trade Center, the US government took a sudden, urgent interest in other seemingly safe arenas that may also be vulnerable to an act of terrorism—including municipal water systems. By 2002, Sandia National Laboratories had begun work on tools to detect poisons in municipal water supplies. The lab continued that work, after president George W. Bush, in 2004, signed Homeland Security Presidential Directive 9 (HSPD-9), which called for more rigorous monitoring and assessment of the country’s water sources and distribution systems.
In 2006, EPA began assembling the first real-world field tests of systems to detect these kinds of attacks, first in Cincinnati, OH, and then in San Francisco, CA; Pittsburgh, PA; Newport News, VA; and northern Kentucky. Results from the Water Quality Event Detection System Challenge were published in April 2013, more than a decade after the government first took interest in the subject.
In that time, the American news cycle has been periodically punctuated by acts of extreme violence, such as the Virginia Tech Massacre and the Boston Marathon Bombing. But no terrorist, vandal, or petty criminal has successfully disrupted daily life by intentionally striking water utilities or water supplies.
Attacks on the nation’s fragmented water system would require a high degree of expertise or investment, and would likely impact only a small portion of the population. Meanwhile, the high price of the technology that would enable highly reliable and comprehensive early detection of such attacks has made them a low priority for water utilities. In total, the low risk of terrorism doesn’t justify the high cost of investing in these systems. But that could suddenly change with a single attack, and anti-terrorism measures in water systems could also yield benefits for more mundane challenges.
Sensors and EDS
In recent years, companies have developed sophisticated in-situ sensors that could help utilities quickly spot and identify contaminants used in terrorist attacks. According to Noah Morgenstern, director of marketing for Whitewater Technologies, the best of these sensors can measure as many as 14 parameters each. However, they fetch a price tag as high as $25,000. Less complicated sensors that measure four parameters each can cost as little as $10,000–but a water system would still need a minimum of three such sensors for them to be fully effective. Depending on how the utility decides to install the sensors, they may also have to lay a bypass pipe for each one.
“It’s a pretty heavy investment,” says Morgenstern.
Should a utility decide to make that investment, the Sensor Placement Optimization Toolkit (SPOT), developed by Sandia National Laboratories, can help identify the optimal number and location for them. According to the lab’s testing, this alone can have a significant impact on handling water contamination events. According to Sandia’s website for its water infrastructure security program, “The estimated reduction on fatalities from high consequence attacks on drinking water was 48%, with a $19B median reduction in estimated value of lives lost.”
Whether sensors track four or 14 parameters, the data is useless without something to interpret the results. That need has been filled both by private companies, as well as government agencies. Sandia and EPA collaborated to create a water quality event detection software program known as CANARY. The program monitors data streaming in from the utility’s sensors. If that data ever ebbs outside of historic norms or preset alert levels, the software issues an alarm.
The software is open source and free for any water utility to download and use, but many utilities may lack the in-house expertise to install and configure this kind of program. Those utilities can hire outside firms to handle the setup of CANARY or any other event detection system, such as BlueBox from Whitewater.
“Any water utility can use a tool like CANARY,” says Kate Klise, a researcher at Sandia National Labs, “the requirements are that you have a water distribution network model, and you have online sensors that are supplying you with information.”
Those sensors don’t necessarily need to be the expensive, sophisticated multi-parameter units that can cost tens of thousands of dollars. Many utilities use SCADA (supervisory control and data acquisition) systems to actively monitor energy use, water pumped and water delivered. The addition of a program like CANARY can help utility managers spot some problems on a rapid turnaround.
For example, when water pipes break and create a situation in which foreign chemicals or particulate could enter the water supply, the utility may not have any immediate warning unless water literally bubbles up to the surface. An event detection system, however, may quickly spot that the amount of water pumped suddenly doesn’t match the amount of water delivered and alert a manager to that fact. Such an arrangement would not, however, tell the utility if that accident actually introduced any foreign matter into the water.
Why Water Utilities Make Bad Targets
According to Morgenstern with Whitewater, water utilities haven’t exactly been immune from attacks in the past decade. A few would-be terrorists have attempted backflow attacks by using a pump with greater pressure than their tap to push their chosen poison into the water supply. Fortunately for the water utility’s other customers, nobody really noticed. The volume of water in the line quickly diluted the chemical to the point that it no longer posed a threat.
This doesn’t mean that such an attack could never be successful. According to Doug McCall, director of marketing for remote sensor seller, Sensus, a plot to poison public waters would take “quite a bit of work and quite a bit of thinking.”
If a terrorist was able to secure a very large volume of poison (perhaps a tanker truck) and pump it in at the right point in the distribution system (perhaps a pump site), they could successfully make toxic the water coming out of customers’ faucets. But the attack would impact a limited population. Even in large cities, the non-connected nature of water systems would cap such an attack’s damage potential.
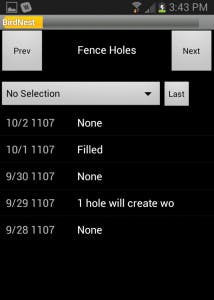
A licensed operator uses BirdNest on his smartphone to collect a combination of operations, compliance, and security information.
“The truth is that most water systems serve far less than one million people,” says Trevor Hill, CEO of Global Water, which owns and operates a collection of water utilities.
When those two facts come together, would-be terrorists have little incentive to make a physical strike on the public water system. The cost of making such an attack is quite high–certainly more than a backpack full of explosives–and the impact is limited.
Accidental Contamination
While the combination of high difficulty and low impact make an intentional attack on a water system unlikely, accidents happen. In 1982, according to a case history from Watts Water Technologies, a crossed pipe in a New England town introduced propane into the municipal water supply. A customer at one five-room home reported that gas bubbled and hissed out of the toilet. That was one of the more minor outcomes of the incident, which resulted in two fires and triggered the evacuation of 500 people.
Fracking, Morgenstern notes, can also cause unintended contamination. While fracking operations are supposed
to vigilantly clean up their wastewater, failure to do so can result in the fracking chemicals getting sucked into nearby municipal water systems. This can lead to the flaming faucet phenomenon that has been profiled in major news outlets including the New York Times.
Other, more common emergencies include chemicals from tanker truck accidents leaching into the water supply, or the ever-possible rupture of an underground pipe that results in mud being swept into the water line.
“Fortunately, water under pressure tends to leak out of pipes not in,” says Hill. But incidents have occurred where the suction of passing water has introduced contaminants.
In cases like these, the tools developed for rapidly responding to terrorist incidents can help mitigate the impacts of simple accidents.
Buttoning Up
While this level of technology may be more than many water utilities are prepared to embrace, a light step into the 21st century could help avoid more mundane issues. According to Gary Lassin, chief operating officer at BirdNest Services, Inc., many water utilities still use “guys carrying paper and pencil log sheets” to do the bulk of their inspections and meter reading.
These sheets have to be transcribed into a computer before any kind of centralized system can spot a problem with the data–presuming that the data was written down correctly and that the workers at the office can read the field worker’s handwriting.
Companies like BirdNest offer mobile applications that allow field workers to enter these readings directly into a centralized system through a smartphone or tablet device. “We help people transition from a pencil and paper world,” says Lassin.
When utilities make the transition to a system like this, it comes with a variety of benefits. First, it eliminates the need to copy over sometimes-illegible handwriting. Second, it helps identify erroneous numbers immediately. If a field worker enters a number that’s outside of preset limits, the program will highlight it. If that number was entered incorrectly, the field worker can correct it. If the number was correct, the worker immediately knows–and can inform his bosses–that something in the system has gone wrong.
While this stands as a significant advancement on its own, these systems can help encourage field workers to be vigilant with more mundane tasks. Utilities that use BirdNest can program the digital log sheet with any number of checklist items–including performing a perimeter check.
This option, Lassin says, was suggested by a customer who maintained a Superfund site where workers had to spot and record any holes in or under the fence where animals might have gotten in. While only a small percentage of BirdNest water utility customers use the system for security reasons, adding this kind of reminder may make sense. It could help protect equipment in remote areas from everything from terrorists to vandals to burrowing animals.
Hacking Meters
Cyber attacks on water systems also often prove to require more effort than they’re worth. Many water systems still rely on old-school technology for their communications infrastructure. As mentioned above, it’s not uncommon for field workers to visit each home, read the meter, and write the reading down on a sheet of paper so that someone back at the office can enter it into a computer.
Some water utilities, though, have modernized their infrastructure to allow them to remotely read and manage their meters. This may be done through radio-enabled vehicles, tower-based networks similar to cellular phone networks, or satellite uplinks. While these modern upgrades open the door for an attack, they only do so by a crack.
In the case of satellite systems, the manner in which the meters communicate with satellites renders rogue signals effectively impossible. In cellular or radio systems, a cyber attacker could intercept the signal coming from the meter or send their own rogue signal to the meter, but the hacker would first have to crack the system’s encryption. That could prove to be a significant challenge. According to Balu Ambady, director of security for Sensus, his company’s wireless water meters, which operate on the cellular spectrum, use a higher level of encryption than most online banking applications.
The reason for this, Ambady says, is because the Sensus sensors could remain deployed for as long as 20 years. Should the encryption standard increase in the next decade, Sensus doesn’t want to have to recall its units.
Even if a hacker should pierce such intense encryption, the most damaging thing they could do is steal data. Spotting which homes aren’t using water could help a criminal network decide which homes to rob. This is certainly a negative outcome, but nothing close to an act of terrorism. In theory, hackers could also disrupt water delivery by shutting off meters en-masse, but the impact would be short-lived and many customers may not even notice. The first customers impacted would inform the utility that their water had stopped. The utility would then be able to quickly turn meters back on–probably before the bulk of customers experienced any disruption.
Other attacks, such as a jamming attack, may be able to prevent a utility from communicating with its network, but this would have no direct impact on water delivery. It would also, according to Ambady, be very easy to spot.
“If they need to hit more than a few meter radius [they are] very easy to triangulate,” he says.
Hacking the Network
Hackers could also bypass a utility’s communication system and directly attack its computer network. According to the famed quote from Federal Bureau of Investigations Director Robert Mueller, “There are only two types of companies: those that have been hacked, and those that will be.”
For this reason, Steve Uban, director of innovation for Informational Data Technologies, says it’s important for water utilities to maintain the same cyber security protocols that all other companies should. His company sells satellite-based water metering services, which lowers the probability of an attack on communication within the network. The signals between meters and the satellite itself are mostly invulnerable, and the uplink stations that directly communicate with the satellite are even protected by military hardware. The online portal between the water utility and IDT, however, isn’t. The usernames and passwords IDT provides work from any internet-connected computer, and the system has no way of knowing the actual identity of the person who entered them.
The biggest risk, Uban says, would be that of a disgruntled former employee using his or her password to log into the system and either steal data or disrupt operations. For that reason, it is important for utilities to vigilantly disable access for any employee who leaves the company.
Utility employees also need to be vigilant with how they handle their login data. While IDT would never send a password and username through e-mail, Uban says, that doesn’t stop employees from e-mailing this information to each other or even themselves. Should a bad actor gain access to that e-mail–either by hacking or simple access–the danger could be greater than that posed by a disgruntled former employee. While the former employee’s access would likely be shut off eventually, a hacker getting regular access to the system through a current employees login could siphon information, undetected, for an extended period of time.
For that reason, Uban says, water utilities should have a robust security policy that includes appropriately complex passwords that are changed on a frequent basis. And, if employees don’t follow the policy, there should be real consequences. “If somebody’s not following that, you want to be able to fire them,” he says, “because it’s a risk to the whole system.”
Even that risk could be minimal, though. In a satellite-managed system, a bad actor could shut off water at each customer’s meter for as long as 12 hours, the period of time during which the satellite is out of communication range. That would be disruptive, but it wouldn’t be destructive.
To cause real havoc, the criminal would have to gain access to primary water valves. According to Hill, these are still often not connected to computer systems. Even when they are, they are usually connected to a secondary, proprietary computer network that would be more difficult to access.
“Hackers of the world are out to create havoc,” says Hill. “I’m sure they can do it, but we go to a fairly great extent to securitize those systems.”
Given the difficulty presented, Ambady says, a hacker that demonstrates the level of skill and determination required to damage those systems would be better served by attacking a major commerce site, like eBay.
Finding Value in Expensive Sensors
While the in-situ sensors mentioned in this article may be too expensive to justify their utility in detecting terrorist attacks or accidental contamination, they could help managers save money on chlorine and other purifying agents.
Chlorine concentrations naturally fluctuate as customers draw more or less water out of the system. Utility managers are generally cautious people, according to Hill, and tend to err on the side of using more chlorine than a system needs. When a pipe ruptures and potentially sweeps foreign contaminants into the water supply, he says, the standard operating procedure for utilities is to “super-chlorinate the downstream legs.”
In many cases, that could be wasting chlorine. As Hill notes, water pressure usually works in favor of utilities in these situations. If a utility manager could check contaminant levels before deploying the purifier, they could often avoid or reduce chlorine usage. The same sensors could help save chlorine on a daily basis. By keeping managers constantly abreast of residual chlorine levels, the utility could deploy only as much chlorine as is needed at any given time.
In the long run, such sensors may also save money on labor costs. At present, according to Morgenstern, sensor readings are not admissible to fulfill government mandated water testing requirements, but that may not always be the case. Should this convention change in the next few years, a suite of sensors may save the utility from needing to hire additional employees tasked with physically checking water samples in the field.
Danger Still Lurks
At present, according to Lassin, Hill, and others, water utilities tend to be reluctant to modernize their operations. In Hill’s observation, utility managers tend to be “risk-averse” and don’t want to gamble their capital budgets on new technology that doesn’t have iron-clad evidence that it will improve their operations.
In Lassin’s view, the water utility industry has little financial incentive to find new efficiencies; each utility has a local monopoly, and its costs–whatever they are–are automatically covered.
But this comfortable atmosphere could rapidly shift if terrorists attacked the water supply in a major city. Despite the low damage potential of such an attack, Klise at Sandia Labs says it could have a significant impact on “public trust.”
“We need water. We need clean water,” she says. “It’s a resource that is undervalued in general.”
Should that happen, it could shock regulators into requiring water utilities to do a better job of monitoring their operations on a constant basis. And that could mean installing in-situ sensors and event detection software.